Tailscale Opens Aperture AI Gateway to Self-Serve: No Waitlist, No Key Sprawl
Tailscale's Aperture AI gateway is now available in self-serve alpha — centralize LLM API keys, track usage by identity, and eliminate key sprawl in minutes.
Tailscale's Aperture AI gateway is now available in self-serve alpha — centralize LLM API keys, track usage by identity, and eliminate key sprawl in minutes.
Tailscale has opened its Aperture AI gateway to self-serve access, dropping the waitlist and letting developers spin up centralized AI credential management in minutes as of March 23, 2026.
The move marks a significant step for the $160M-backed networking company as it pushes beyond its core VPN product into AI infrastructure security — a category that barely existed 18 months ago.
"AI adoption is moving faster than security teams can keep up," Tailscale wrote in the launch announcement. The company is targeting a specific and increasingly common failure mode: API key sprawl.
Most teams start simple. A developer generates an LLM provider key, drops it in a .env file, and ships. Then that key migrates into a CI pipeline. Then a container. Then an agent runtime. Each step feels small — until a key ends up in a public repository or an agent starts taking actions nobody authorized.
"These spreading credentials aren't just assets, they're infrastructure," Tailscale noted. Security teams end up tracking, rotating, and auditing keys scattered across machines and services, with no clear picture of who or what is using them.
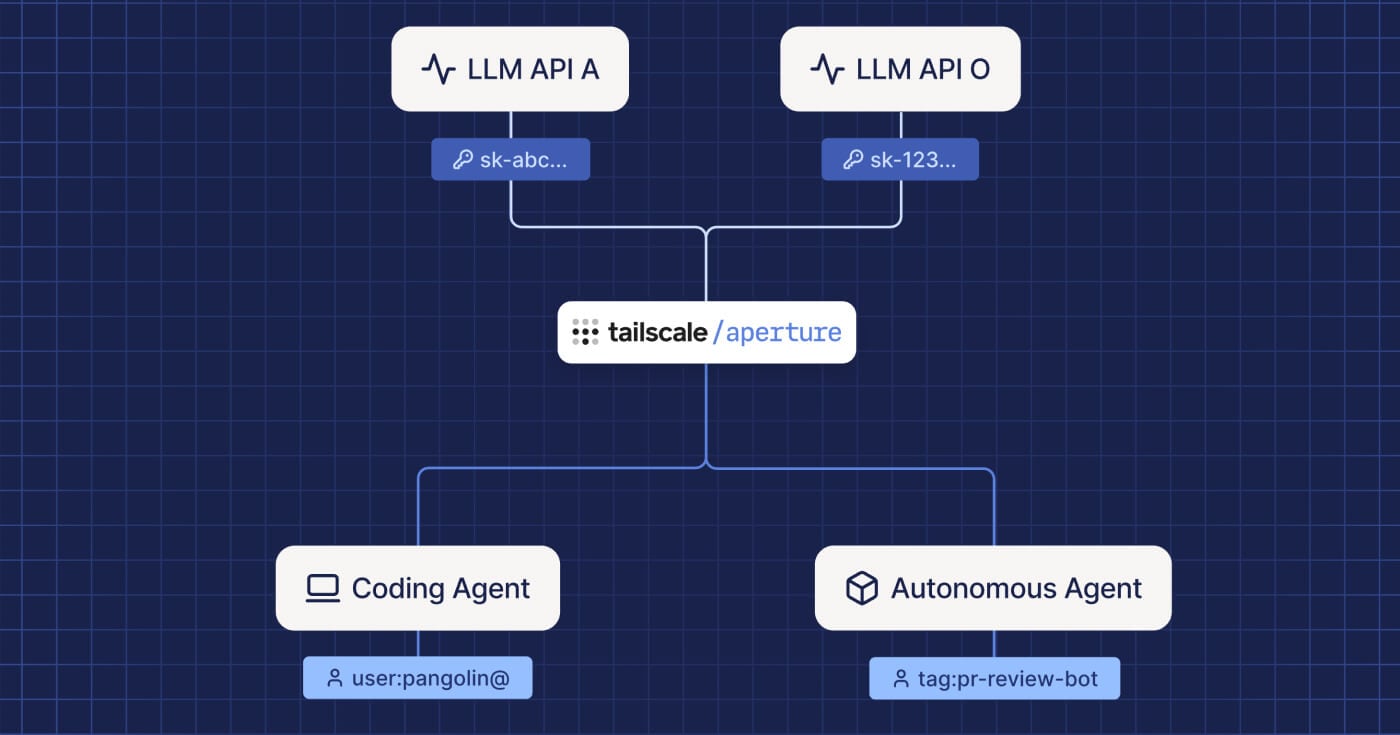
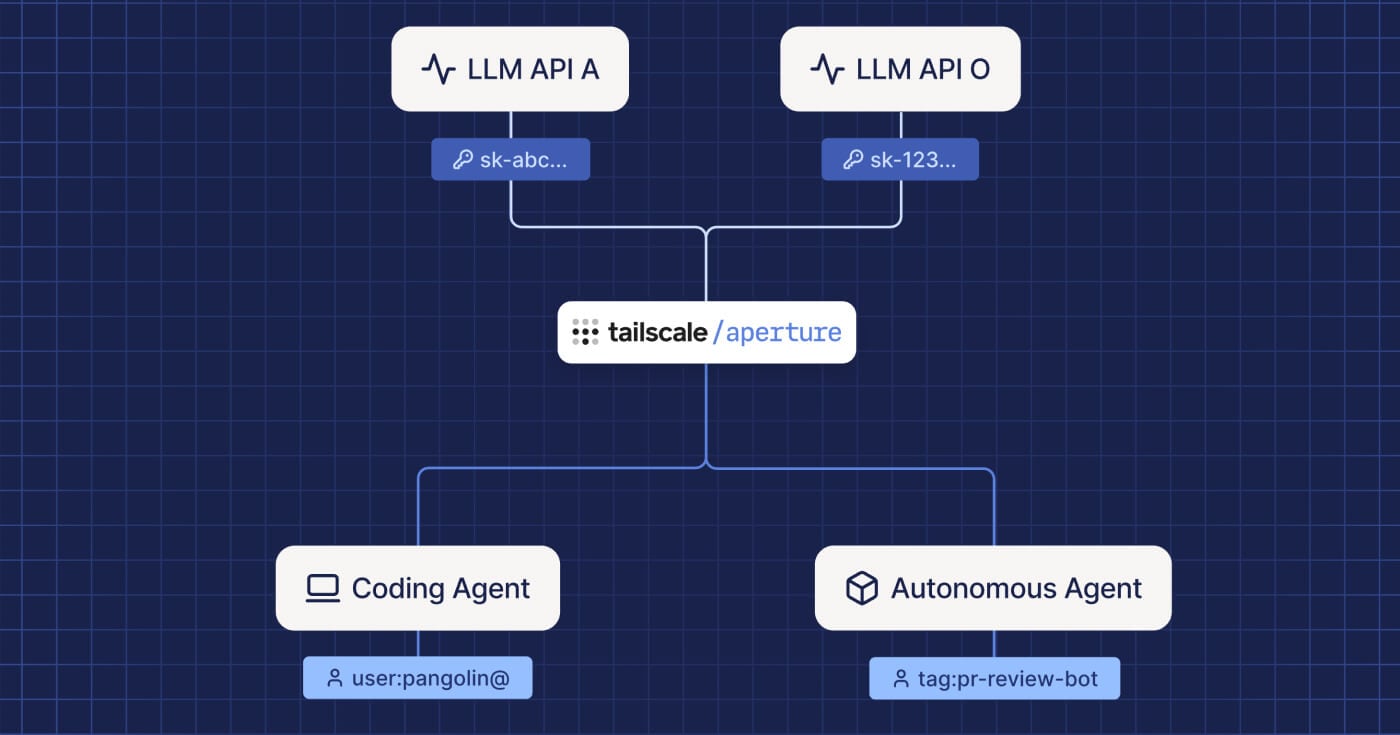
Aperture sits between your infrastructure and LLM providers as an identity-aware gateway. Instead of embedding API keys in applications, credentials stay inside the gateway. Requests arrive authenticated through Tailscale identity, and Aperture forwards them with the correct provider key.
The architecture shifts two things simultaneously: where credentials live and how usage is tracked. Because every request flows through a single point, platform teams gain visibility into which teams are using AI, which models and tools are being called, and where costs are concentrating — all tied to identity rather than an anonymous key.
Developers get a cleaner workflow too. They can experiment and build without storing sensitive credentials on their machines. Platform and security teams get a central place to observe access, apply guardrails, and audit activity across users, services, and agents.
Aperture can be purchased as a standalone product, separate from paid Tailscale plans.
Tailscale originally launched Aperture in private alpha earlier in 2026, requiring approval before access. The self-serve opening removes that friction entirely.
The company is treating this as an early-stage signal-gathering exercise. "This is an early alpha release of an experimental product," Tailscale wrote. "It's still a work in progress, so pieces may be incomplete, features may change, and you may experience bugs. We're sharing it to learn and gather feedback."
Teams interested in production deployments are advised to contact aperture@tailscale.com before going live.
"Tailscale is sort of the shovel seller for the AI world." — Avery Pennarun, Co-Founder and CEO, Tailscale (Accel, April 2025)
Tailscale recorded a webinar on Aperture with partners from Cribl, Oso, and AWS/Amazon Bedrock alongside CEO Avery Pennarun. The session covers how Aperture routes AI frontends and backends, contains key sprawl, and extends security monitoring into AI usage. It's now available on demand.
Tailscale raised a $160M Series C led by Accel in April 2025, with AI infrastructure cited as a growth driver. The company had crossed 10,000 customers at the time of the raise, and Accel noted a surge in demand from AI startups using Tailscale to manage networking across multi-cloud workloads.
Aperture represents Tailscale's direct play on the AI security layer. The AI gateway market is nascent but filling quickly — organizations building agentic systems need something between their infrastructure and LLM providers that handles authentication, visibility, and control without requiring every developer to manage credentials directly.
Aperture is in early alpha and will evolve based on user feedback. The key signals to watch: whether Tailscale moves from alpha to general availability on a defined timeline, how the pricing model develops relative to paid Tailscale plans, and whether the partner ecosystem (Cribl, Oso, AWS Bedrock) deepens into tighter integrations.
For teams already on Tailscale, the friction to try Aperture is now essentially zero. For teams not on Tailscale, the gateway is a new entry point into the broader ecosystem — which is likely part of the calculus behind removing the waitlist entirely.

A zero-human company (ZHC) is a business where AI agents handle every operational function without human employees. Learn how it works, real examples earning $6M+ ARR, the tech stack, and a step-by-step guide to building one in 2026.

OpenAI rolled out Chronicle for its Codex macOS desktop app, an opt-in research preview that captures periodic screenshots and stores text summaries locally so Codex understands what a developer is working on without being told each time.

Anthropic's Claude Managed Agents launches in public beta, promising to cut AI agent deployment from months to days with managed cloud infrastructure and built-in orchestration.